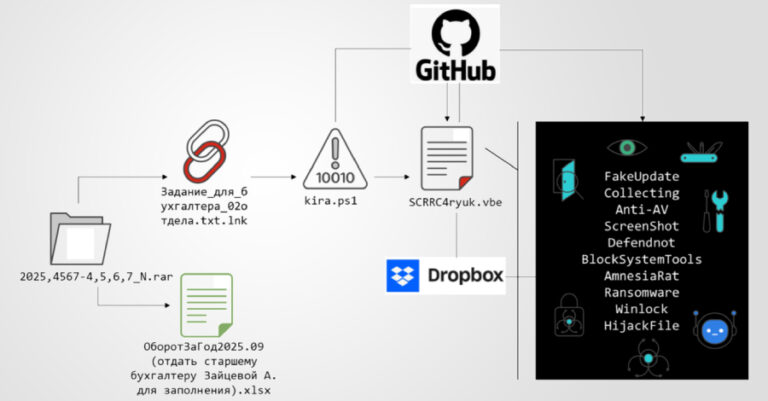
Neglected Domains Used in Malspam to Evade SPF and DMARC Security Protections
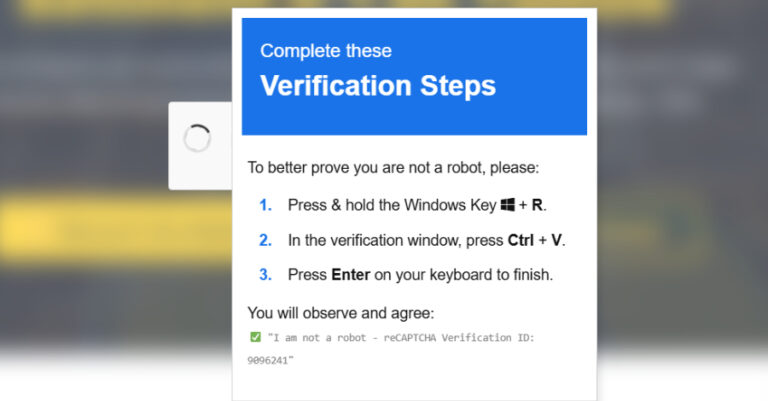
Cybersecurity researchers have found that bad actors are continuing to have success by spoofing sender email addresses as part of various malspam campaigns. Faking the sender address of an email is widely seen as an attempt to make the digital missive more legitimate and get past security mechanisms that could otherwise flag it as malicious….