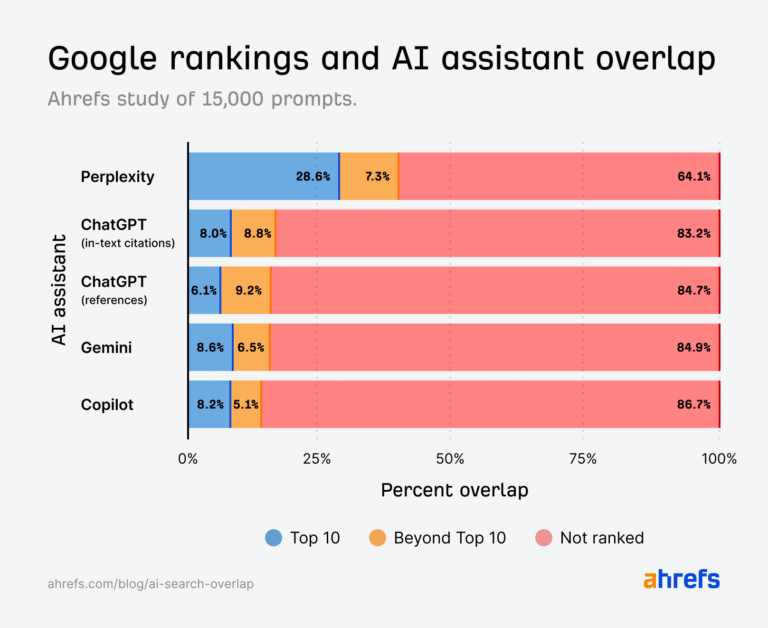
81 AI SEO Statistics for 2025 (Fresh and Original Data)
It pays to know how AI is changing search. 32% of Nasdaq companies see a strong correlation between their search visibility and stock prices. (Source) If traffic from search goes up, so do their stock prices. But recently, many companies saw major traffic (and revenue) declines thanks to changes in AI search. This post is…